Methods for Preventing Brute Force Attacks
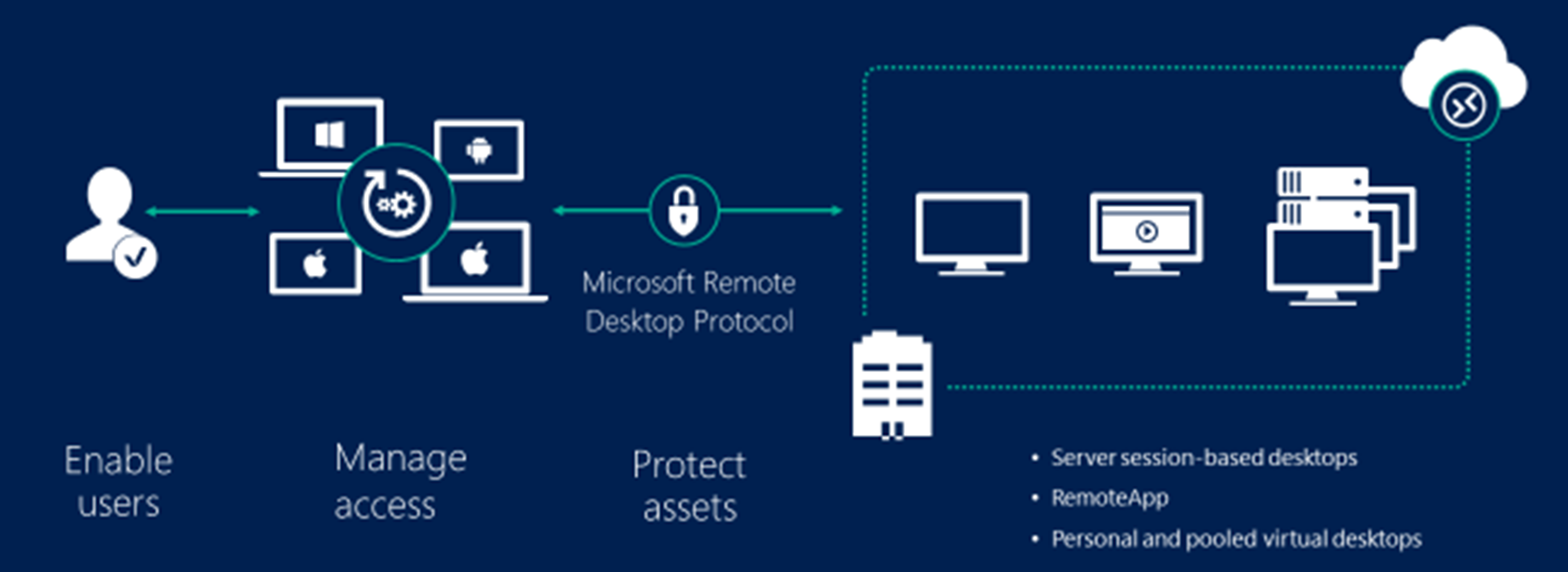
Every experienced network administrator or server security expert understands that leaving the RDP or remote desktop protocol port exposed to the internet or using a weak password exposes the network to cyber threats. This article will describe how to avoid brute force attacks on windows servers.
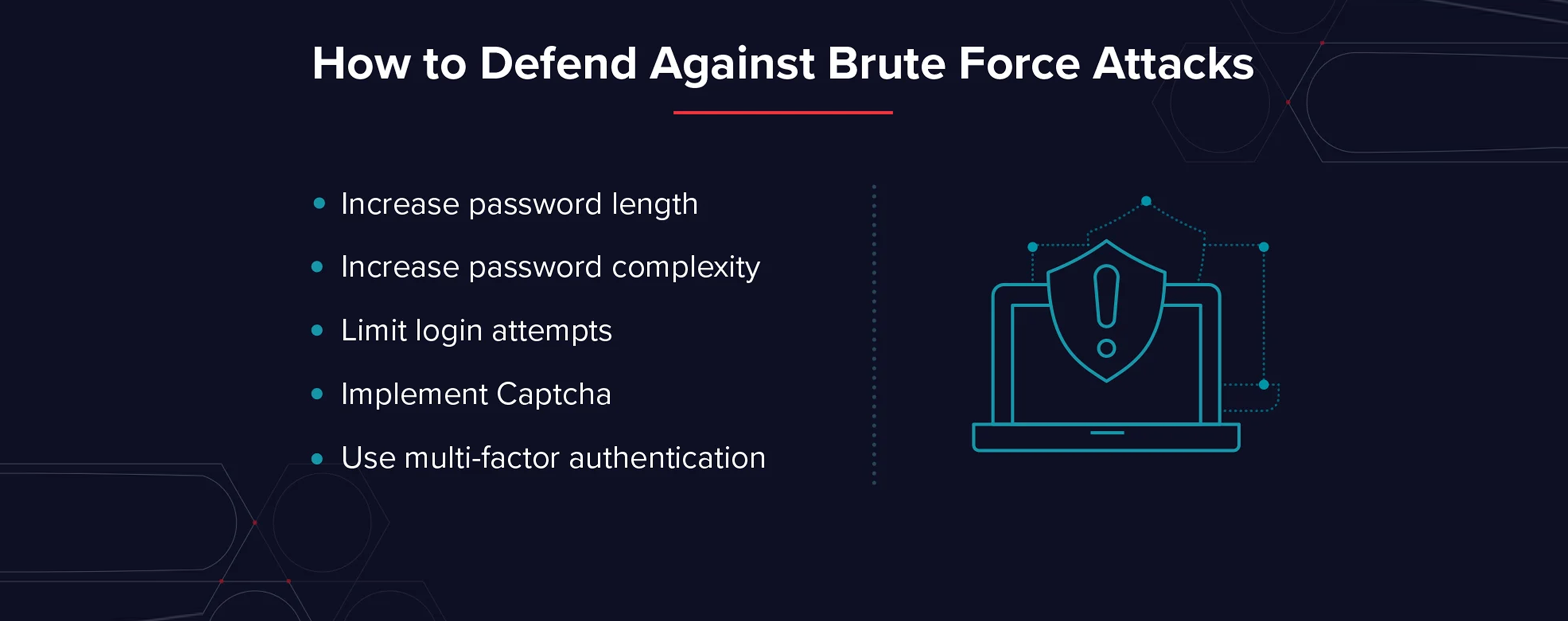
How to Defend Against Brute Force Attacks?
Hackers utilize various methods to gain access to a computer, network, website, or other online services. A brute force attack is one of the easiest and most time-consuming methods of hacking a server or system. Some advantages of the brute force attack technique include testing network security and recovering stolen passwords
 Methods for Preventing Your Windows Server From Brute Force Attacks
Methods for Preventing Your Windows Server From Brute Force Attacks
Defend Windows Server against Brute Force Attacks, The following is a list of advice for you if you wish to prevent or block Brute Force Attacks on Windows Server. The tips are as follows:

The first recorded use of the term "phishing" was in the cracking toolkit AOHell created by Koceilah Rekouche in 1995; however, it is possible that the term was used before this in a print edition of the hacker magazine 2600.
1 : CREATE A STRONG PASSWORDThis is the first and most essential step in making an account; you must enter a strong password in a complex fashion that no one can guess. If hackers try your password, don't give them any information about your password, username, or id. Don’t associate your password with your personal information, such as your age, date of birth, or name. Examine the windows password policy.
 2 : Control the Number of Failed Login Attempts
2 : Control the Number of Failed Login Attempts
As you may already be aware, brute force attacks work similarly. as a result, numerous failed efforts will occur. You can feel guaranteed that the attack will not succeed if you limit failed login attempts. The 'account lockouts with increasing delays' feature are also available. In this manner, your account will be shut after a fixed number of failed tries, making things much easier for the network administrator.
 3 : Install an Efficient Intrusion Prevention Tool
3 : Install an Efficient Intrusion Prevention Tool
By installing the tools, we can keep an eye on our server or computer; also, we can analyze and control the attack if there are many failed attempts with a particular IP or set of IPs. It then blocks that ip for two hours, slowing down the rate of attacks. If you wish to make certain exceptions or change the block time, you can do so byconfiguring the program.
 How can I detect if my server is being brute-forced?
Some Useful Tips :
How can I detect if my server is being brute-forced?
Some Useful Tips :
-
Check your server logs to see if your computer or server is under brute force attack.
-
You’re under a brute force attack if you see a lot of failed login attempts.
-
Suppose a single IP address or even numerous IP addresses make a lot of failed attempts in a short period.
-
In that case, you should immediately examine your client’s IPs and immediately block them if you determine that these IPs are those of attackers.



